Why Your WAF is Failing: Engineering an OWASP-Aligned Pentest Engine for WordPress
Stop "Installing" Security. Start Architecting It.
As developers, we’ve all heard the joke: "WordPress is just a collection of vulnerabilities held together by PHP." While the core has matured, the ecosystem hasn't. Most "security plugins" are reactionary—they block an IP after the probe has already happened.
When I built the SEOSiri Shield, I wanted to move away from "Checkbox Marketing" and toward Proactive Hardening. I wanted a tool that didn't just tell me a site was "safe," but showed me the raw results of an automated penetration test.
The Problem: The "Black Box" of Plugin Security
Most plugins act as a black box. They claim to "protect" you, but they don't provide a quantifiable security score based on industry standards. If you can't measure your attack surface, you can't secure it.
The Solution: The 19-Test OWASP Pentest Engine
In the Pro and Agency tiers of the Shield, we integrated an automated testing suite mapped directly to the OWASP Top 10 2021 Framework.
We aren't just blocking common patterns; we are systematically probing the installation for:
Broken Access Control: Checking for exposed sensitive paths (like .env or wp-config.php.bak).
Injection Surfaces: Testing how the WAF handles complex SQLi and XSS payloads before they hit the database.
Cryptographic Failures: Auditing SSL/TLS configurations and security headers (HSTS, CSP).
Vulnerable Components: Cross-referencing active plugins against the latest CVE feeds from WPScan and Abuse.ch.
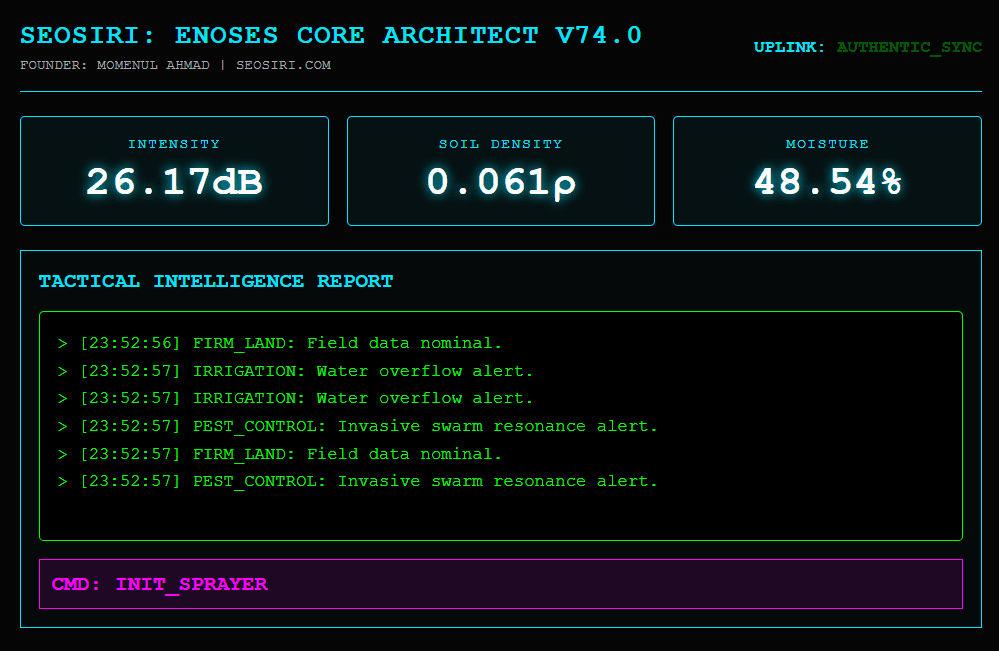
Under the Hood: The "SEO 2 DevOps" Pipeline
For the developers here, the Shield isn't just a UI dashboard. We’ve built it to integrate into a modern workflow:
Pre-Bootstrap Blocking: Our WAF hooks into the plugins_loaded or earlier mu-plugins cycle to drop malicious requests before WordPress even initializes its heavy objects.
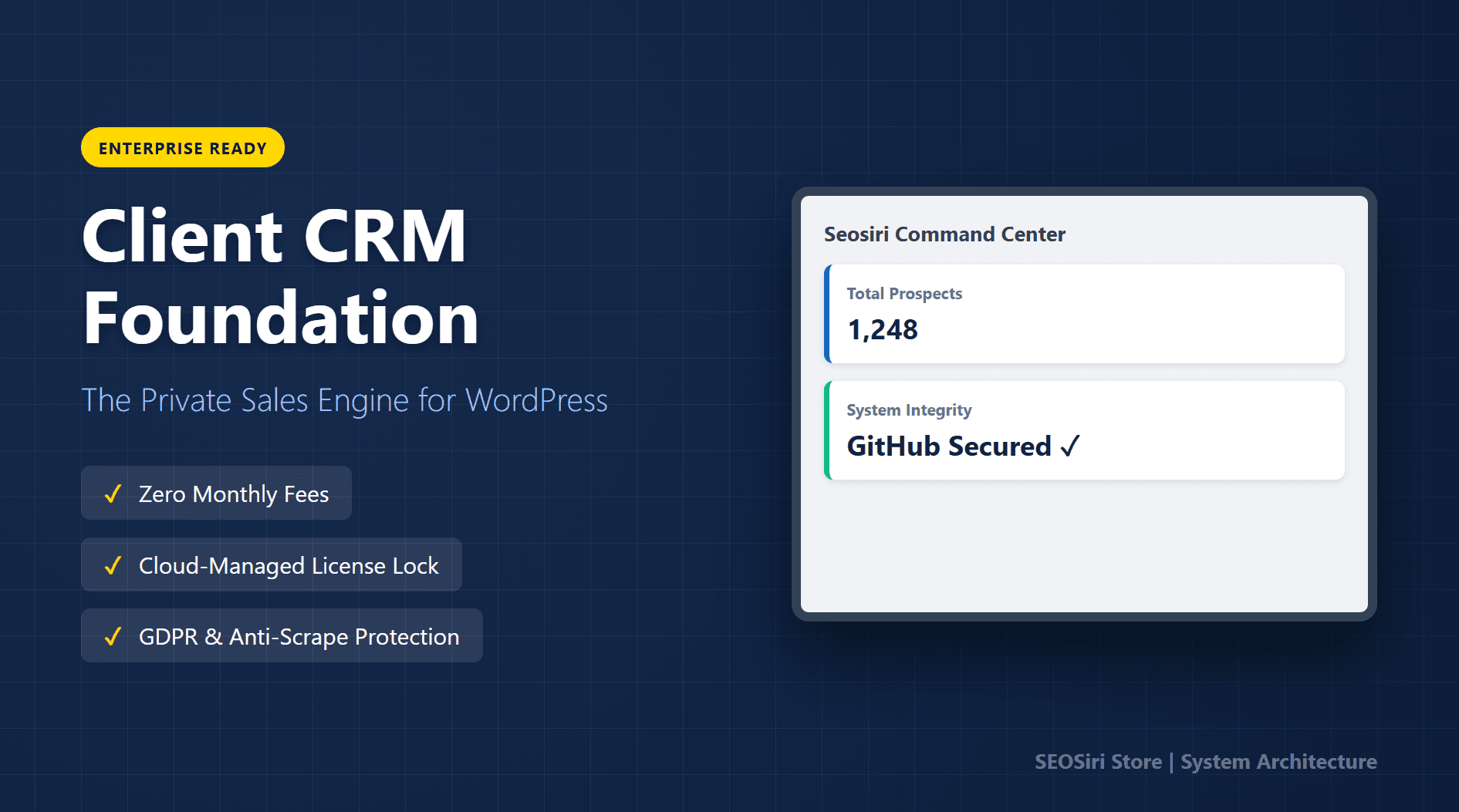
REST API Endpoints: The Agency tier exposes security event data via REST API, allowing you to pull logs into your own custom monitoring dashboards or centralized SOC.
Slack/Discord Webhooks: Get real-time JSON payloads for critical events (like a modified core file or a brute-force lockout) directly in your dev channel.
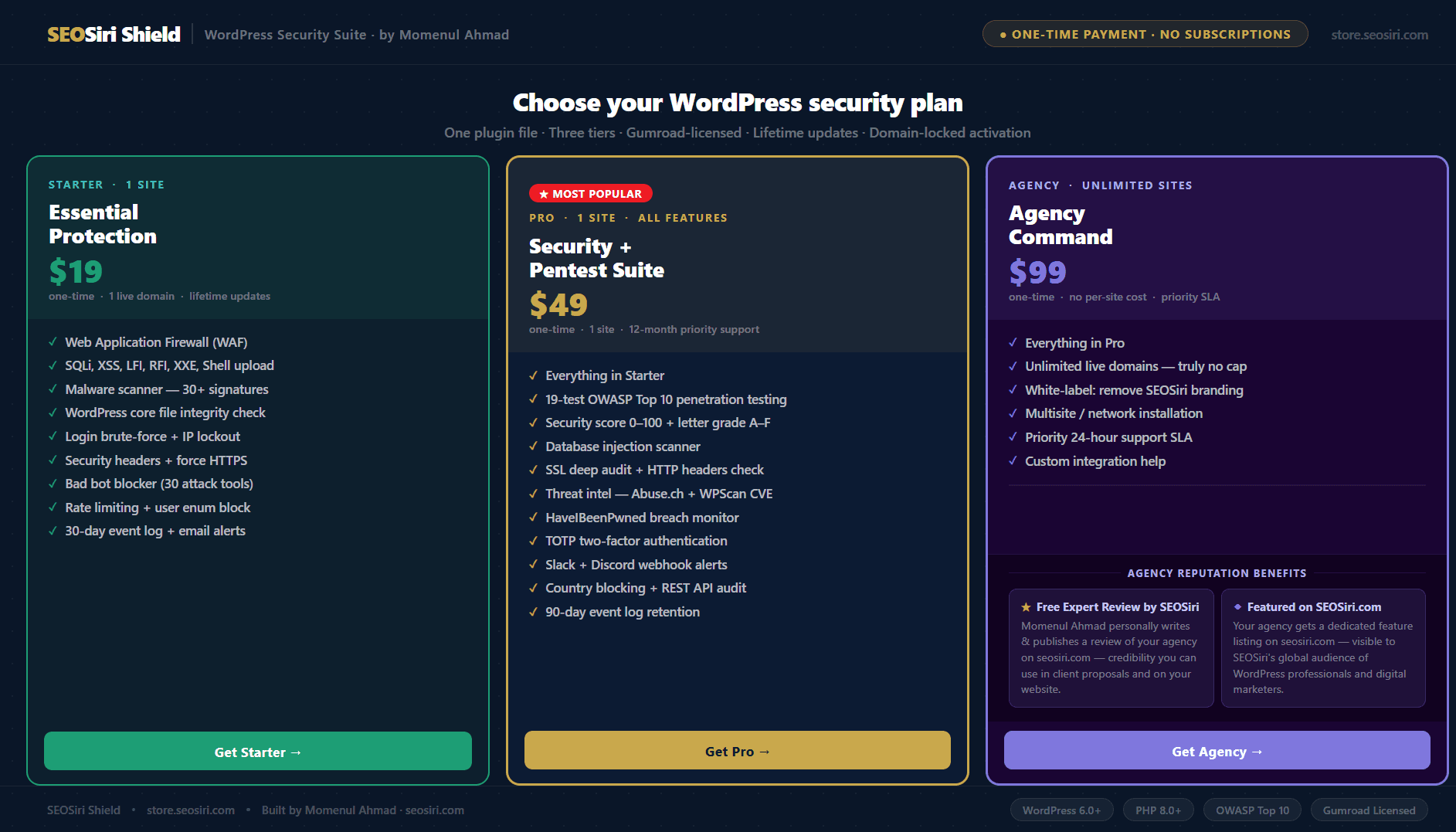
The "Anti-SaaS" Pricing Model
We’ve all seen the trend: a simple security plugin that suddenly costs $199/year. For a developer or a small agency, those subscriptions eat your margins.
I built the Shield on a One-Time Payment model. You buy the code, you own the protection.
Starter ($19): For the lean solopreneur.
Pro ($49): For the engineer who needs the Pentest Suite and 2FA.
Agency ($99): Unlimited sites, White-label mode, and REST API access.
Final Thoughts for Devs
Security is a primary pillar of AEO (Answer Engine Optimization). In 2026, if an AI agent detects an insecure header or a malware signature, your site is "dead air."
Stop guessing. Run a real pentest. Get a score. Fix the bugs.
Technical Documentation:
Read the full implementation guide here: SEOSiri WordPress Security Plugin Shield Technical Guide
Secure Your Stack:
I'm Momenul Ahmad, founder of SEOSiri. I'm hanging out in the comments—let's talk WAF logic and OWASP implementations.